Malwarebytes anti-malware
Содержание:
- Mobile adware
- What is malware?
- What is cybersecurity?
- How Malwarebytes Premium protects you
- All about spyware
- All about malware
- The future of cybersecurity programs (which is already here)
- How to characterize a Trojan
- How does anti-malware work?
- History of spyware
- How can I protect myself from malware?
- Что умеет хакерское Malware
- Возможности Malwarebytes Anti-Malware Free
- What is the history of malware?
- History of Trojans
- Как самому проверить компьютер на зараженность Malware
- Who do spyware authors target?
Mobile adware
There’s not much real estate room on a mobile’s screen. So when a mysterious icon moves into your start
screen, or scads of ads start clogging your notification bar, you’ve probably got an uninvited adware guest.
No big surprise, since thousands of Android apps now contain the gift that keeps on shoving icons and ads at you
without warning.
There are two methods through which mobiles come down with adware: through the browser and through downloaded
applications.
-
Infection by browser refers to a known exploit, caused by the way most browsers handle redirections executed by JavaScript code. It’s a weakness that can cause ad pop-ups; and advertising affiliates know about it, and how to exploit it. If your mobile’s browser has been compromised, then the best way to block the pop-ups is to use a different browser, disable JavaScript, or install a browser with ad blocking. Another remedy to pop-ups is to back out of them using Android’s back key. Or you can clear your history and cache, which will also stop the ads from coming back.
- Infection by downloaded applications refers to getting infected with persistent ads through adware apps
installed on a phone. They present in different forms, from full screen ads inside and outside of the infected
app, to the device notifications and on the lock screen. Typically, a third-party app store installs this kind
of adware app. So it’s best to avoid third-party app stores, although even Google Play has been an
unwitting source of adware-infested apps.
Despite its being an annoying pest, take some small comfort in the fact that such adware is generally not blatantly
malicious, threatening your device like malware might. Many of the free apps you download to your phone often
include third-party ad content, providing software developers an alternative revenue stream so you can have their
offering for free. Still, adware is not generally benevolent; so faced with a free app that stuffs your device with
adware, and a paid program that plays nicely, consider the best choice for you.
What is malware?
Malware, or “malicious
software,” is an umbrella term that describes any malicious program or code that is harmful to systems.
Hostile, intrusive, and intentionally nasty, malware seeks to invade, damage, or disable computers, computer
systems, networks, tablets, and mobile devices, often by taking partial control over a device’s operations.
Like the human flu, it interferes with normal functioning.
Malware is all about making money off you illicitly. Although malware cannot damage the physical hardware of systems
or network equipment (with one known exception—see the Google Android section below), it can steal, encrypt, or
delete your data, alter or hijack core computer functions, and spy on your computer activity without your knowledge
or permission.
What is cybersecurity?
Cybersecurity, or computer security, is a catchall term for any strategy for protecting one’s system from malicious attacks aimed at doing things like hold your computer hostage, steal system resources (as in a botnet) record your passwords and usernames, and a whole host of other bad things. Such attacks might occur via your hardware (like a backdoor) or through your software (like an exploit).
Cybersecurity threats and their countermeasures are varied and nuanced nowadays, but the marketplace naturally strives for simplicity when communicating to consumers. This is why many people still see “viruses” as the biggest threat to their computer. In reality, computer viruses are just one type of cyberthreat that happened to be popular when computers were in their infancy. They’re far from the most common threat today, but the name stuck. It’s a bit like calling every disease a cold.
“For the most part, antivirus and anti-malware mean the same thing. They both refer to software designed to detect, protect against, and remove malicious software.”
How Malwarebytes Premium protects you
At Malwarebytes, we are serious about infection prevention, which is why we aggressively block both websites and advertisements that we consider fraudulent or suspicious. For example, we block torrent sites like The Pirate Bay. Though many savvy users have used such sites without issue, some of the files they offer for download are really Trojans. For similar reasons, we also block cryptomining through browsers, but the user can choose to turn off the block and connect.
Our reasoning is that it’s better to err on the side of safety. If you want to take the risk, it’s easy to whitelist a site, but even tech-savvy types can fall for a convincing Trojan.
To learn more about Trojans, malware, and other cyberthreats, check out the Malwarebytes Labs blog. The things you learn may just help you avoid an infection down the road.
All about spyware
When you go online, don’t assume that your privacy is secure. Prying eyes often follow your activity—and your personal information—with a pervasive form of malicious software called spyware. In fact, it’s one of the oldest and most widespread threats on the Internet, secretly infecting your computer in order to initiate a variety of illegal activities, including identity theft or a data breach. It’s easy to fall prey to and can be hard to get rid of, especially since you’re most likely not even aware of it. But relax; we’ve got your back with all you need to know about what spyware is, how you get it, what it tries to do to you, how to deal with it, and what to do to avoid future spyware attacks.
All about malware
You know how every year the medical community campaigns for everyone to get a flu shot? That’s because flu
outbreaks typically have a season—a time of year when they start spreading and infecting people.
In contrast, there are no predictable seasonal infections for PCs, smartphones, tablets, and enterprise networks.
For them, it’s always flu season. But instead of suffering chills and body aches, users can fall ill from a
kind of machine malady—malware.
Malware infections come at us like a torrent of water from a fire hose, each with its own methods of attack—from
stealthy and sneaky to subtle like a sledgehammer. But if knowledge is power, as a preventative inoculation against
infection, we offer here a short course on malware, what it is, its symptoms, how you get it, how to deal with it,
and how to avoid it in the future.
The future of cybersecurity programs (which is already here)
Artificial intelligence (AI) and machine learning (ML) are the latest stars in anti-malware technology.
AI allows machines to perform tasks for which they are not specifically pre-programmed. AI does not blindly execute a limited set of commands. Rather, AI uses “intelligence” to analyze a situation, and take action for a given goal such as identifying signs of ransomware activity.
ML is programming that’s capable of recognizing patterns in new data, then classifying the data in ways that teach the machine how to learn.
Put another way, AI focuses on building smart machines, while ML uses algorithms that allow the machines to learn from experience. Both these technologies are a perfect fit for cybersecurity, especially since the number and variety of threats coming in every day are too overwhelming for signature-based methods or other manual measures. Both AI and ML are still in developmental phases, but they hold immense promise.
In fact, at Malwarebytes, we already use a machine-learning component that detects malware that’s never been seen before in the wild, also known as zero-days or zero-hours. Other components of our software perform behavior-based, heuristic detections—meaning they may not recognize a particular code as malicious, but they have determined that a file or website is acting in a way that it shouldn’t. This tech is based on AI/ML and is available to our users both with real-time protection and on-demand scanning.
In the case of business IT professionals with multiple endpoints to secure, the heuristic approach is especially important. We never know what the next big malware threat will be. So heuristics plays an important role in Malwarebytes Endpoint Protection, as does AI and ML. Together, they create multiple layers of protection that address all stages of the attack chain for both known and unknown threats.
How to characterize a Trojan
People sometimes think of a Trojan as a virus or a worm, but it is really neither. A virus is a file infector which can self-replicate and spread by attaching itself to another program. Worms are a type of malware similar to viruses, but they don’t need to be attached to another program in order to spread. Most viruses are now seen as legacy threats. Worms have also become rare, though they do pop up from time to time.
“A Trojan can be like a Swiss Army knife of hacking.”
Think of Trojans as an umbrella term for malware delivery, because there are various kinds of Trojans. Depending on the criminal programmer’s intent, a Trojan can be like a Swiss Army knife of hacking—acting as a bit of standalone malware, or as a tool for other activities, such as delivering future payloads, communicating with the hacker at a later time, or opening up the system to attacks just as the Greek soldiers did from inside the Trojan fortress.
Put another way, a Trojan is a delivery strategy that hackers use to deliver any number of threats, from ransomware that immediately demands money, to spyware that conceals itself while it steals valuable information like personal and financial data.
Keep in mind that adware or PUPs (potentially unwanted programs) can be confused with Trojans because the delivery method is similar. For example, sometimes adware sneaks onto your computer as part of a bundle of software. You think you’re downloading one piece of software, but it’s really two or three. The program authors usually include the adware for marketing affiliate reasons so they can monetize their installer with offers—usually clearly labeled. Such adware bundlers are typically less malicious than Trojans. Also, they do not conceal themselves as Trojans do. But since the adware distribution vector resembles that of a Trojan, it can cause confusion.
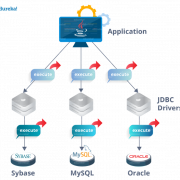
How does anti-malware work?
The old school method of signature-based threat detection is effective to a degree, but modern anti-malware also detects threats using newer methods that look for malicious behavior. To put it another way, signature-based detection is a bit like looking for a criminal’s fingerprints. It’s a great way to identify a threat, but only if you know what their fingerprints look like. Modern anti-malware takes detection a step further so it can identify threats it has never seen before. By analyzing a program’s structure and behavior, it can detect suspicious activity. Keeping with the analogy, it’s a bit like noticing that one person always hangs out in the same places as known criminals, and has a lock pick in his pocket.
This newer, more effective cybersecurity technology is called heuristic analysis. “Heuristics” is a term researchers coined for a strategy that detects threats by analyzing the program’s structure, its behavior, and other attributes.
Each time a heuristic anti-malware program scans an executable file, it scrutinizes the program’s overall structure, programming logic, and data. All the while, it looks for things like unusual instructions or junk code. In this way, it assesses the likelihood that the program contains malware.
What’s more, a big plus for heuristics is its ability to detect malware in files and boot records before the malware has a chance to run and infect your computer. In other words, heuristics-enabled anti-malware is proactive, not reactive. Some anti-malware products can also run the suspected malware in a sandbox, which is a controlled environment in which the security software can determine whether a program is safe to deploy or not. Running malware in a sandbox lets the anti-malware look at what the software does, the actions it performs, and whether it tries to hide itself or compromise your computer.
Another way heuristic analytics helps keep users safe is by analyzing web page characteristics in order to identify risky sites that might contain exploits. If it recognizes something fishy, it blocks the site.
In brief, signature-based antivirus is like a bouncer at the nightclub door, carrying a thick book of mug shots and booting anyone that matches. Heuristic analysis is the bouncer who looks for suspicious behavior, pats people down, and sends home the ones carrying a weapon.
“Heuristics is a term researchers coined for a strategy that detects viruses by analyzing the program’s structure, its behavior, and other attributes.”
History of spyware
As with much Internet discourse, it’s difficult to pin down exactly where “spyware” as a word and a concept originated. Public references to the term date back to Usenet discussions happening in the mid-90s. By the early 2000s, “spyware” was being used by cybersecurity companies, in much the same way we might use the term today; i.e. some sort of unwanted software program designed to spy on your computer activity.
In June 2000, the first anti-spyware application was released. In October 2004, America Online and the National Cyber-Security Alliance performed a survey. The result was startling. About 80% of all Internet users have their system affected by spyware, about 93% of spyware components are present in each of the computers, and 89% of the computer users were unaware of their existence. Out of the affected parties, almost all, about 95%, confessed that they never granted permission to install them.
At present, and in general, the Windows operating system is the preferred target for spyware applications, thanks largely to its widespread use. However, in recent years spyware developers have also turned their attention to the Apple platform, as well as to mobile devices.
How can I protect myself from malware?
Stay vigilant. Pay particular attention if you see a domain name that ends in an odd set of letters, i.e., something
other than com, org, edu, or biz, to name a few, as they can be an indicator for risky websites.
“Make sure your operating system, browsers, and plugins are always up to date.”
For all your devices, pay close attention to the early signs of malware infection to prevent them from burrowing in.
Make sure your operating system, browsers, and plugins are always up to date, because keeping your software patched
can keep online criminals at bay.
For mobile users, only download apps from Google Play Store (the App Store is the iPhone’s only choice). Every
time you download an app, check the ratings and reviews first. If it has a low rating and a low number of downloads,
it is best to avoid that app.
Do not download apps from third-party sources. The best way to make sure of this is to turn off this function on
your Android phone. Go to Settings on your Android device and open up the Security section. Here, make sure Unknown
Sources is disabled to avoid installation of apps from marketplaces other than the Play Store.
To keep their businesses safe, organizations can prevent malicious apps from threatening their networks by creating
strong mobile security policies and by deploying a mobile security solution that can enforce those policies. This is
vital in the business environment that exists today—with multiple operating systems at work under multiple roofs.
Finally, get yourself a good anti-malware program. It should include layered protection (the ability to scan and detect malware such as adware and spyware while maintaining a proactive real-time
defense that can block threats such as ransomware). Your security program should also provide remediation to correct
any system changes from the malware it cleans, so everything goes back to normal.
So before you take a hit on your PC, mobile, or enterprise network, hit back first by downloading a quality cybersecurity and antivirus program, such as Malwarebytes for Windows, Malwarebytes for Mac, Malwarebytes for Android, Malwarebytes for Chromebook, Malwarebytes for iOS, portable Malwarebytes, or one of Malwarebytes’ business products. (It’s a good idea to get that flu shot too!)
Что умеет хакерское Malware
Есть несколько основных разновидностей вредоносных программ:
- Кейлоггеры;
- Удалённое управление (RAT);
- Шифровальщики-вымогатели;
- Майнеры;
- Ботнеты.
Кейлоггеры (key – клавиша, log – журнал действий) записывают в log-файл все нажатия клавиш на клавиатуре и отправляют информацию хакеру. С помощью специальных алгоритмов не сложно вычленить из набора данных логины, пароли и другую конфиденциальную информацию. Если вы не вводите пароли руками, а пользуетесь менеджерами паролей с шифрованием и не являетесь политиком, бизнесменом или знаменитостью, то можете отделаться лёгким испугом.
Куда «интереснее» дела обстоят с RAT («крысы», в простонародье). RAT-malware хакеры используют для получения полного контроля над операционной системой. Может вы сталкивались с удалённой помощью техподдержки, например с помощью программы TeamViewer? Это когда компьютерщик из другого здания/города/страны подключается к вашему компьютеру, водит мышкой, запускает программы и закачивает файлы. Согласитесь, неприятно было бы осознать, что последние несколько месяцев какая-то «крыса» делала тоже самое с вашим компьютером в ваше отсутствие.
Вымогатели наделали шуму 2017 году, во время криптовалютного бума. Заразив компьютер, вирус зашифровывал документы или все данные так, что прочитать их было невозможно. Далее нужно было выслать хакеру выкуп в криптовалюте: биткоины или эфириум. Криптовалюты использовались из-за их анонимности и безнаказанности злоумышленника. Выслав выкуп, никакого ключа для расшифровки данных пользователи не получали.
Майнеры используют вычислительную мощность процессора и видеокарты для добычи криптовалют. Майнинг это очень ресурсоёмкий вычислительный процесс, поэтому хакерам нужно как можно больше заражённых компьютеров. Прямого вреда майнеры не наносят и можно долго не замечать его присутствие.
Умный майнер может не сильно загружать процессор, когда вы работаете за компьютером, чтобы подольше оставаться не замеченным, но зато вовсю «кочегарить», в ваше отсутствие. В любом случае, компьютер начинает тормозить, шуметь и греться. Потом приходит «интересный» счёт за электроэнергию, а оборудование может преждевременно выйти из строя.
Ботнеты также используют ресурсы компьютера, но не только вычислительные, работа компьютера может не измениться заметно. Вот что хакеры делают с ботнетами:
- Используют вычислительную мощность для подбора паролей к нужным ресурсам и файлам методом перебора;
- Устраивают DDoS атаки в интернете, т.е. отправляют с вашего компьютера миллионы запросов на атакуемый ресурс;
- Используют компьютер как прокси-сервер, для личных или коммерческих целей. Прокси-сервер позволяет хакеру выйти в интернет от лица вашего компьютера/города/страны, примерно так же, как через VPN;
- Рассылают почтовый спам;
- Взламывают другие компьютеры.
Со временем, алгоритмы антиспама блокируют ваш IP-адрес, и ваши письма, отосланные с помощью почтового клиента, попадают в папку «СПАМ», не доходя до адресатов. Также, можете замечать на некоторых сайтах предложение пройти проверку на «ты не робот?» перед тем, как откроется главная страница. Но это не всегда означает что вы заражены ботнетом, может быть заражён другой компьютер в сети провайдера.
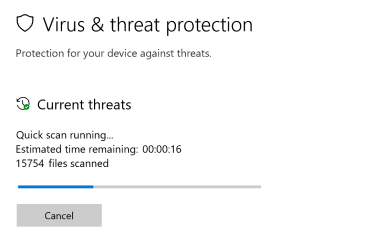
Возможности Malwarebytes Anti-Malware Free
- Удаление вредоносных программ как автоматически, так и в ручном режиме;
- Интеллектуальный эвристический анализ помогает удалять не явные вредоносные объекты;
- Программа обнаружения отличается качественными анти шпионскими модулями;
- В бесплатной версии, имеется встроенный блокировщик подозрительных веб-ресурсов;
- Быстрое сканирование системы с настраиваемым списком игнорирования;
- Реализована защита режиме реального времени — технология Real Time Protection;
- Способность работать в ускоренном режиме;
- Удаление вредоносного ПО в реальном времени;
- Эффективное помещение инфицированных файлов в карантин с последующей опцией восстановления.
Преимущества
- Поддерживается любая актуальная операционная система Windows, начиная от XP, Vista, заканчивая Windows 10;
- Антивирусная программа весьма быстро обнаруживает и удаляет вредоносные приложения;
- Современный и простой интерфейс, имеет русский язык оболочки;
- Возможность настройки для обеспечения максимально оптимизации и производительности;
- Отсутствуют какие-либо конфликты, если на ПК установлены другие антивирусы;
- Отличная система поиска и удаления червей, троянов и различного вредоносного программного обеспечения;
- Содержит передовую технологию Malwarebytes Chameleon, которая препятствует отключению антивируса сложными угрозами;
- В комплект с Malwarebytes Anti Malware Free Antivirus Software входят дополнительные утилиты;
- Антивирусные сканеры и базы сигнатур, стабильно обновляются с официального сайта Malwarebytes Corporation;
- Malwarebytes Anti Malware рекомендуют специалисты по информационной безопасности PC, Mac и других авторитетных ресурсов.
Недостатки
What is the history of malware?
Given the variety of malware types and the massive number of variants released into the wild daily, a full history
of malware would comprise a list too long to include here. That said, a look at malware trends in recent decades is
more manageable. Here are the main trends in malware development.
The 1980s and onward: The theoretical underpinning of “self-reproducing automata”
(i.e., viruses) dates back to an article published in 1949, and early viruses occurred on pre-personal computer
platforms in the 1970s. However, the history of modern viruses begins with a program called Elk Cloner, which started
infecting Apple II systems in 1982. Disseminated by infected floppy disks, the virus itself was harmless, but it
spread to all disks attached to a system, exploding so virulently that it can be considered the first large-scale
computer virus outbreak in history. Note that this was prior to any Windows PC malware. Since then, viruses and worms
have become widespread.
The 1990s: The Microsoft Windows platform emerged this decade, along with the flexible macros of
its applications, which led malware authors to write infectious code in the macro language of Microsoft Word and
other programs. These macro viruses infected documents and templates rather than executable applications, although
strictly speaking, the Word document macros are a form of executable code.
2002 to 2007: Instant messaging worms—self-replicating malicious code spread through an instant
messaging network—take advantage of network loopholes to spread on a massive scale, infecting the AOL AIM network,
MSN Messenger, and Yahoo Messenger, as well as corporate instant messaging systems.
2005 to 2009: Adware attacks proliferated, presenting unwanted advertisements to computer screens,
sometimes in the form of a pop-up or in a window that users could not close. These ads often exploited legitimate
software as a means to spread, but around 2008, software publishers began suing adware companies for fraud. The
result was millions of dollars in fines. This eventually drove adware companies to shut down.
2007 to 2009: Malware scammers turned to social networks such as MySpace as a channel for delivering rogue advertisements, redirects, and offers of fake antivirus and security tools. Their ploys were designed to dupe consumers through social engineering tricks. After MySpace declined in popularity, Facebook and Twitter became the preferred platforms. Common tactics included presenting fake links to phishing pages and promoting Facebook applications with malicious extensions. As this trend tapered down, scammers explored other means to steal.
2013: A new form of malware called ransomware launched an attack under the name CryptoLocker, which continued from early September 2013 to late May 2014, targeting computers running Windows. CryptoLocker succeeded in forcing victims to pay about $27 million by the last quarter of 2013. Moreover, the ransomware’s success spawned other similarly named ransomware. One copycat variant netted more than $18 million from about 1,000 victims between April 2014 and June 2015.
2013 to 2017: Delivered through Trojans, exploits, and malvertising, ransomware became the king of
malware, culminating in huge outbreaks in 2017 that affected businesses of all kinds. Ransomware works by encrypting
the victim’s data, then demanding payments to release it.
2017 to Present: Cyptocurrency—and how to mine for it—has captured widespread attention, leading to
a new malware scam called cryptojacking, or the act of secretly using someone else’s device to surreptitiously
mine for cryptocurrency with the victims’ resources.
History of Trojans
Fun and games
A program called ANIMAL, released in 1975, is generally considered the world’s first example of a Trojan attack. It presented itself as a simple game along the lines of twenty questions. However, behind the scenes, the game copied itself onto shared directories where other users could find it. From there, the game could spread across entire computer networks. For the most part, it was a harmless prank.
In the 1990s, another infamous Trojan appeared disguised in the form of a simple Whack-A-Mole game. The program hid a version of NetBus, a program that allows one to remotely control a Microsoft Windows computer system over a network. With remote access, the attacker could do any number of things to a computer, even open its CD tray.
Love and money
Through the 2000s, Trojan attacks continued to evolve, as did the threats they carried. Instead of targeting people’s curiosity, Trojans leveraged the rise of illegal downloading, disguising malware as music files, movies, or video codecs. In 2002, a Windows-based backdoor Trojan horse called Beast emerged and was capable of infecting almost all versions of Windows. Then, in late 2005, another backdoor Trojan called Zlob was distributed disguised as a required video codec in the form of ActiveX.
The 2000s also saw a rise in the number of Mac users, and cybercriminals followed suit. In 2006, the discovery of the first-ever malware for Mac OS X, a low-threat Trojan Horse known as OSX/Leap-A or OSX/Oompa-A, was announced.
The motivations behind Trojan attacks also began to shift around this time. Many early cyberattacks were motivated by a lust for power, control, or pure destruction. By the 2000s, an increasing number of attacks were motivated by greed. In 2007, a Trojan named Zeus targeted Microsoft Windows in order to steal banking information by means of a keylogger. In 2008, hackers released Torpig, also known as Sinowal and Mebroot, which turned off anti-virus applications, allowing others to access the computer, modify data, and steal confidential information like passwords and other sensitive data.
Bigger and badder
As cybercrime entered the 2010s, the greed continued, but hackers started thinking bigger. The rise of untraceable cryptocurrencies like Bitcoin led to a rise in ransomware attacks. In 2013, the Cryptolocker Trojan horse was discovered. Cryptolocker encrypts the files on a user’s hard drive and demands a ransom payment to the developer in order to receive the decryption key. Later that same year, a number of copycat ransomware Trojans were also discovered.
“Many of the Trojans we hear about today were designed to target a specific company, organization, or even government.”
The 2010s have also seen a shift in how victims are targeted. While many Trojans still use a blanket approach, attempting to infect as many users as possible, a more targeted approach seems to be on the rise. Many of the Trojans we hear about today were designed to target a specific company, organization, or even government. In 2010, Stuxnet, a Windows Trojan, was detected. It was the first worm to attack computerized control systems, and there are suggestions that it was designed to target Iranian nuclear facilities. In 2016, Tiny Banker Trojan (Tinba) made headlines. Since its discovery, it has been found to have infected more than two dozen major banking institutions in the United States, including TD Bank, Chase, HSBC, Wells Fargo, PNC, and Bank of America. In 2018, the Emotet Trojan, once a banking Trojan in its own right, was seen to be delivering other types of malware, including other Trojans.
As one of the oldest and most common ways to deliver malware, the history of Trojans follows the history of cybercrime itself. What started as a way to prank one’s friends morphed into a way to destroy networks, steal information, make money, and seize power. The days of pranks are long gone. Instead, they continue to be serious cybercriminal tools used mostly for data stealing, espionage, and Distributed Denial of Service DDoS attacks.
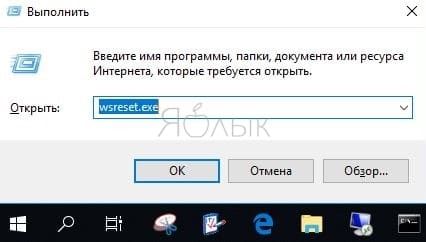
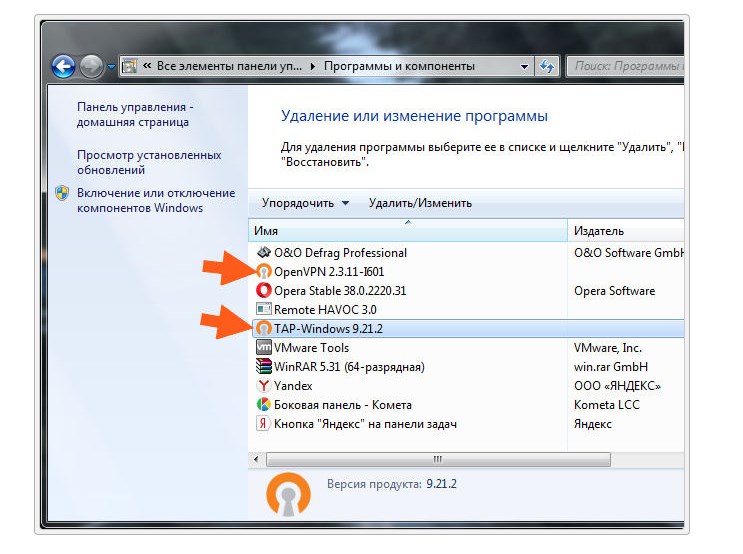
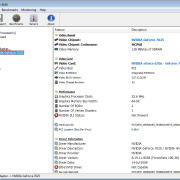
Как самому проверить компьютер на зараженность Malware
Резидентные программы — это такие процессы, которые работают и остаются в памяти после их исполнения. Такая форма дает возможность программе Malware иметь постоянный доступ к данным и, не спуская глаз, следить за всеми происходящими в системе событиями.
Помогут обнаружить резидентного Malware в памяти обычные системные утилиты, такие, как менеджер задач – Task Manager, вызываемый комбинацией клавиш Ctrl+Alt+Del. После ее вызова появится диалоговое окно, где в виде списка отобразятся все работающие на текущий момент задачи. Нужно проверить этот перечень на предмет наличия в нем резидентного процесса с присоединенным Malware.
Риск самостоятельного выполнения такой манипуляции по незнанию довольно высокий
Закрытие важной резидентной программы, которая критично влияет на системную работу, может вызвать даже «синий экран смерти» или запустить перезагрузку. Ответить однозначно на вопрос о том, действительно ли конкретная резидентная программа не относится к работе системы, даже не всем профессионалам и гикам под силу
Можно поковыряться в руководстве по ОС, или поискать незнакомую программу из списка менеджера задач в интернете. Если по результатам поисковых мероприятий вы не нашли ничего существенного, или каких-либо указаний на то, что перед вами зловредный Malware, лучше не трогайте этот процесс.
Malware очень часто берет себе имена процессов, которые чрезвычайно похожи на имена стандартных процессов. В данном случае глядя на него, вы можете подумать, что это нормальный процесс, однако это будет не так. К примеру, вместо процесса WSOCK23.dll, который отвечает за обработку функций сокетов, можно увидеть поддельный процесс WSOCK33.dll. Другие варианты предусматривают похожие формы подмены, похожие на те, которые используются при фишинге сайтов, когда визуально символы похожи друг на друга и их подмена на первый взгляд не видна. Например, KERNE132.dll – на самом деле будет подделкой, тогда как в правильном процессе вместо 1 (единицы) должна стоять буква L – KERNEL32.dll. Правильное местонахождение этого файла – в папке Windows\System32, но некоторые Malware кладут его в другое место – в папку Windows\System.
Можно удостовериться, не зависла ли в памяти уже закрытая программа, в том месте, где ее уже давно быть не должно.
Еще может быть вариант, когда программа в памяти держит несколько копий себя, хотя никакого сервиса на текущий момент с таким названием пользователь не запускал.
Закройте все приложения, и если после этого, проверяя объем занятой памяти, вы видите, что какой-то сервис занял почти все ресурсы, его стоит проверить, и особенно это подозрительно, если активность памяти такого ресурса никак нельзя просчитать.
Unlike some other types of malware, spyware authors do not really target specific groups or people. Instead, most spyware attacks cast a wide net to collect as many potential victims as possible. And that makes everyone a spyware target, as even the slightest bit of information might find a buyer.
“Spyware attacks cast a wide net to collect as many potential victims as possible.”
Information obtained through stolen documents, pictures, video, or other digital items can even be used for extortion purposes.
So, at the end of the day, no one is immune from spyware attacks, and attackers usually care little about whom they are infecting, as opposed to what they are after.